
Current Issue
Analysing the Integration of AES-256 Encryption and HMAC Hashing in IoT Smart Healthcare Systems
Eterigho Okpomo Okpu1 1and Onate Egerton Taylor2 2
11Department of Cyber Security, Delta State University of Science & Technology,Ozoro,Delta State, Nigeria.
22Department of Computer Science, Rivers State University,Port-Harcourt, Rivers State, Nigeria.
11email: okpuoe@dsust.edu.ng,, 2email: taylor.onate@ust.edu.ng.
---------------------------------------------------------- ------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------
ABSTRACTThe exponential growth of Internet of Things (IoT) technology has been a driving force in the development of smart healthcare systems, facilitating patient monitoring and clinical decision support. It uses IoT-enabled medical devices and wearable sensors under the umbrella of Internet of Medical Things (IoMT) to continuously monitor health from afar. Yet, the fundamental security weaknesses of IoT structure and the high sensitivity of medical data reveal serious security and privacy problems. Therefore, this research suggests a comprehensive security framework to provide the confidentiality, integrity, and authenticity of data transmission in IoMT ecosystems. At the physical layer, the framework utilizes AES-256 encryption and HMAC (Hash-based Message Authentication Code) hashing to minimize cyber threats and prevent unauthorized access. The only additionalcomputation cost at any performance evaluation is negligible, but we gain a lot more in terms of security on the data. The findings confirm the seeing of implementation and demonstration of a feasible security model to protect the multifarious healthcare architecture from ever- existing threats createdby the number of cyber-attacks.
Keywords:AES-256 Encryption, Cyber Threats, Data Security, HMAC Hashing, Internet of Things (IoT), Internet of Medical Things (IoMT), Patient Monitoring, Privacy Protection, Smart Healthcare Systems, Wearable Sensors.
1. INTRODUCTIONCryptography, the study and application of techniques that protect data and communication from adversaries, guarantees, among other things, information nonrepudiation, confidentiality, integrity,and authenticity. To secure sensitive data, modern cryptographic techniques (such as hashing algorithms like HMAC; symmetric encryption like AES [1]). Advanced Encryption Standard (AES) is the most adopted standard for data protection and secure communication in many digital platforms. AES replaced theolder Data Encryption Standard (DES) which was vulnerable to brute force attacks [2]. AES employs a symmetric-key method [3], in which one key is used for both encryption and decryption. HMAC generates a unique fixed-size hash value called a tag by hashing the message to be authenticated with a secret key using hashing functions like MD5 or SHA-256. HMAC ensures the data integrity by computing a tag that will depend on the content of the message and the secret key. Acco rding to [4], HMAC is strongly resistant to various attacks such as manipulation and impersonation. SHA-256 is a cryptographic hash function from the secure hash algorithm (SHA) family. It aims to return a 256-bit fixed-size output irrespective of the input length [5]. The course was the Diffie-Hellman key exchange, which allowed two parties to derive a shared secretkey over an unsecured channel, significantly changing without reason to communicate securely. In the Diffie-Hellman key exchange, two parties called Jackie and Ahmed share public values generated by their
individual secret keys. This study comes forth to tackle the privacy and security problems in IoMT surroundings, especially in the context of remote patient monitoring systems. This provides an efficient framework to secure data about IoT-enabled medical device equipment and also enhances security in smart healthcare systems. We do this with AES-256 encryption and HMAC hashing at the physical layer.
Researchers oncerns regarding how some encryption algorithms can help protect the protected health information (PHI) [6]. This also covered the connection of patient data, metering data and diagnosis and methods of information security and data integrity. The viability of this strategy in the protection of healthcare data, along with its benefits over other methodologies and the state of its integration in the system, are discussed in the conclusion of this study. [7] analyzes existing works in the domain of E-Health but in a methodical and comprehensive manner. They discuss at length ABE frameworks oriented towards healthcare and evaluate them based on a set of descriptive criteria. The authors then organize them across ten different domains and sub-domains, offering observations and potential recommendations
A brand-new Lionized Remora Optimization-Based Serpent (LRO-S) encryption technique is proposed by [8] in 2023 to secure sensitive data and lessen privacy violations and cyberattacks from hackers and unauthorized users. Combining an enhanced security algorithm with hybrid metaheuristic optimization is the LRO-S technique. Researchers are always looking for appropriate lightweight ciphers for certain applications, which have led to a constant evolution in the field of cryptography techniques for IoT device security [9]. [9] Emphasized that in order to overcome security vulnerabilities in cloud computing, new cryptographic algorithms must be developed. The scalability and security of the LORENA approach for symmetric-key generation in IoHT settings were demonstrated by [10]. A range of MAC-based techniques have been investigated in other studies, including those by [4] and [11], to guarantee data authenticity and integrity. Furthermore, [12] strengthened security against MITM attacks by combining RSA cryptography with DH key exchange. Together, these efforts highlight how crucial it is to incorporate reliable cryptography methods into Internet of Things systems in order to reduce security threats.
An overview of cryptography, or the practice of secure communication in the presence of other parties, is given in [13]. It attempts to hinder eavesdroppers from comprehending the conversation. [14] States that the author addresses the use of the matrix decomposition method and Laplace transform to hyperbolic functions in cryptography. The latch-type voltage sensitive amplifier used in [15] AES secret key generation structure uses the Strong-ARM latch-type sensitive amplifier difference structure as PUF. Galois field multiplier system is used for encryption transformations in the AES engine with real-time S-box production [16]. AES is employed in the suggested secure system to encrypt medical data, according to [17]. AES guarantees the safe conversion of readable data into unreadable forms. AES is a component of hybrid encryption that was suggested for use with medical data by [18]. The suggested AES-based approach enhances data integrity and security. For data security, hybrid encryption employs ECC, Serpent, and AES. The security and data integrity of IoT healthcare data are enhanced by this solution.
A combination of 3DES and LSB was suggested in [19] for the security of medical data. The integration of 3DES and LSB for enhanced security was achieved through the creation of a Java simulation application. A suggested method secures medical data by using mutual authentication. In [20], the researchers presented a hybrid architecture that combined the OpenStack private cloud platform with Cryptography as a Service (CaaS). With the help of this architecture, cloud clients can operate cryptographic operations and deploy keys in the cloud without interference from cloud providers. Two cryptographic approaches are compared and examined by [21]. The first cryptographic approach combines the AES-256 encryption algorithm to preserve data confidentiality with the HMAC-SHA-256 hashing approach to ensure data integrity. The AES-GCM (Galois/Counter Mode) technology, which provides assurance of integrity and confidentiality in a single, integrated process, is used in the second strategy. In the context of healthcare applications, searchable encryption (SE) is described in [22] research, which also categorizes SE use cases into four situations. Then, in
accordance with various EHR retrieving scenarios and requirements, the writers gave a thorough overview of the four representative SE techniques: searchable symmetric encryption (SSE), public key encryption with keyword search (PEKS), attribute-based encryption with keyword search (ABKS), and proxy re-encryption with keyword search (PRES).
The system places a strong emphasis on the confidentiality and integrity of healthcare communication. For safe transfer, it additionally offers a mutual authentication and session key exchange mechanism [23]. [24] State that the Diffie Hellman key exchange was suggested as a means of protecting the transfer of medical data. To authenticate the shortest path for data transfer, a probabilistic neural network was employed. The Diffie Hellman key exchange was employed in the encryption and decryption procedures. MACs guarantee message authentication and data integrity in telemedicine applications, according to [25]. The data integrity and message authentication in telemedicine applications were highlighted by the SHA2 algorithm optimized for MAC construction in Java for security. A Secured framework using the SHA-512 algorithm for integrity assurance was carried out in [26]. System security is improved by the Improved ECC with secret key. The correlation coefficient of the proposed IECC is around 0.045, and the encryption and decryption times are 1.032 μs and 1.004 μs, respectively.
3. METHODOLOGY
In order to guarantee the integrity and confidentiality of private information gathered by wearable health monitoring devices, the integration of HMAC hashing and AES-256 encryption must be done as follows:
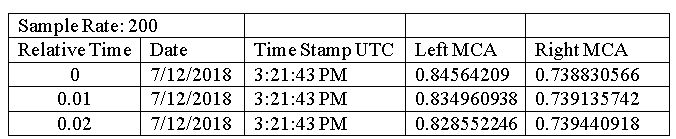
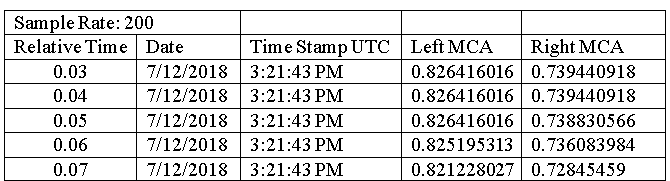
- Data Identification: Identify the health information that wearables are collecting that has to be encrypted. We utilize "TCD_data," a dataset from physionet.org that includes measurements of blood flow velocity in the main arteries of the brain, for this investigation.
- AES Configuration: AES-256 is selected due to its great security. A 256-bit key is used in this symmetric-key approach for both encryption and decryption.
- Key Generation: Create strong encryption keys that are safely kept on wearable technology and unavailable by unauthorized individuals.
- Data Encryption: Before sending sensitive health data over communication channels, encrypt it with AES-256.
- MAC Computation: To ensure data integrity and authenticity, use HMAC-SHA256 to create a MAC over the encrypted data. This procedure is facilitated by the PyCryptodome framework.
- Secure Transmission: Provide other systems, including cloud servers or healthcare platforms, with encrypted health data in a secure manner.
- Data Decryption: After gaining access to the encrypted health data, re-compute the MAC by implementing decryption capabilities in the recipient systems with the appropriate AES-256 keys. If both the computed and acquired MACs match, it indicates that the data was not changed during communication.
- Key Management: To avoid unwanted access or disclosure of encryption keys, implement key creation, distribution, rotation, and revocation protocols.
- Testing and Validation: To guarantee the security framework's efficacy and resilience, thoroughly test and validate it.
To further strengthen the security of the suggested system, the practical implementation uses the [27] Diffie-Hellman key exchange method to securely create shared secret keys via dubious communication channels. An example of the SUBJ001 dataset in usage is shown in Table 1. These datasets on blood pressure were gathered from physionet.org.
4. RESULT AND DISCUSSION
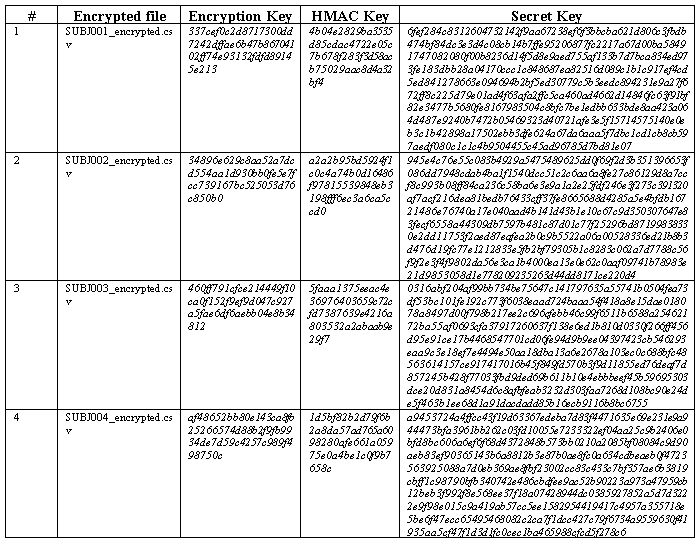
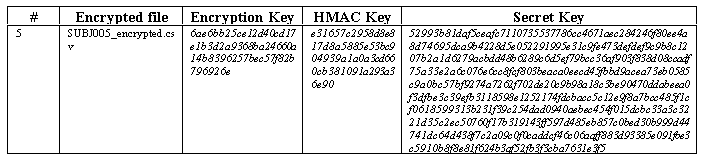
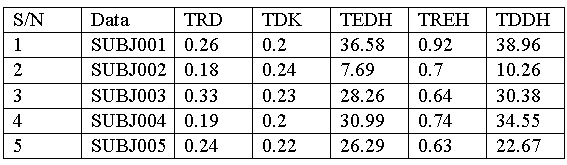
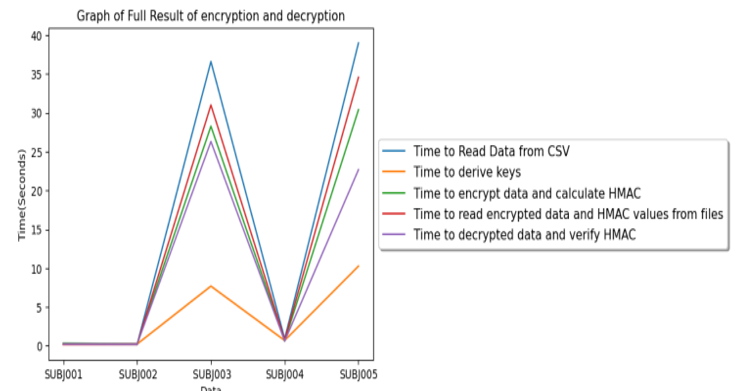
Table 2 showed the encrypted results with the alphabet serving as the secret key. This displays the secret key, the HMAC key, the encryption key, and the encrypted file. The whole encryption and decoding result were shown in Table 3. TRD stands for Time to Read Data from CSV, TDK for Time to Derive Keys, TEDH for Time to Encrypt Data and Compute HMAC, TREH for Time to Read Encrypted Data and HMAC Values from Files, and TDDH for Time to Decrypt Data and Verify HMAC are all displayed in these tables. TRD, TDK, TEDH, TREH, and TDDH scores in SUBJ001 data are, in order, 0.26 seconds, 0.20 seconds, 36.58 seconds, 0.92 seconds, and 38.96 seconds. The complete encryption and decoding results were displayed graphically in Figure 1. The results of hashing, decrypting, and encrypting data using the AES 256 and HMAC techniques are shown in Figure 1.
5. CONCLUSION
This study applies the HMAC hashing approach to verify data integrity at the physical layer of IoMT and integrates the AES-256 encryption technique to assure data secrecy there as well. Python was used as the programming language to create the system. TRD, TDK, TEDH, TREH, and TDDH scores for file SUBJ001 are 0.26 seconds, 0.20 seconds, 36.58 seconds, 0.92 seconds, and 38.96 seconds, in that order. The results of this study will improve safe IoT smart healthcare systems and offer insightful information to practitioners and researchers alike.
DECLARATIONS:| Acknowledgments | : | Not applicable. |
| Conflict of Interest | : | The authors declares that there is no actual or potential conflict of interest about this article. |
| Consent to Publish | : | The authors agree to publish the paper in the Global Research Journal of Social Sciences and Management. |
| Ethical Approval | : | Not applicable. |
| Funding | : | Author claims no funding was received. |
| Author Contribution | : | Both the authors confirms their responsibility for the study, conception, design, data collection, and manuscript preparation. |
| Data Availability Statement | : | The data presented in this study are available upon request from the corresponding author. |
REFERENCES
- Arunkumar, J. R., Velmurugan, S., Chinnaiah, B., Charulatha, G., Prabhu, M. R., & Chakkaravarthy, A. P. (2023). Logistic Regression with Elliptical Curve Cryptography to Establish Secure IoT, Computer Systems Science & Engineering, 46(1).
- Wang, J., Han, J., Li S., Zhou, F., & Wang, N., (2024). A Lightweight Combined Physical Layer Encryption and Authentication Scheme for Industrial Internet of Things, IEEE Access.
- Kumar, C., Prajapati, S. S., & Verma, R. K. (2022). A Survey of Various Lightweight Cryptography Block ciphers for IoT devices, In 2022 IEEE International Conference on Current Development in Engineering and Technology (CCET), 1-6, IEEE.
- Devi, S., Kuruba, C., Nam, Y., & Abouhawwash, M. (2023). Paillier Cryptography Based Message Authentication Code for IoMT Security, Computer Systems Science & Engineering, 44(3), DOI: 10.32604/csse.2023.025514.
- Katulić, F., Sumina, D., Groš, S., & Erceg, I. (2023). Protecting Modbus/TCP-Based Industrial Automation and Control Systems Using Message Authentication Codes, IEEE access.
- Abhishek, Tripathy, H. K., & Mishra, S. (2022). A succinct analytical study of the usability of encryption methods in healthcare data security, In Next Generation Healthcare Informatics (pp. 105-120). Singapore: Springer Nature Singapore.
- Imam, R., Kumar, K., Raza, S. M., Sadaf, R., Anwer, F., Fatima, N., & Rahman, O. (2022). A systematic literature review of attribute based encryption in health services, Journal of King Saud University-Computer and Information Sciences, 34(9), 6743-6774.
- Almalawi, A., Khan, A. I., Alsolami, F., Abushark, Y. B., & Alfakeeh, A. S. (2023). Managing security of healthcare data for a modern healthcare system, Sensors, 23(7), 3612.
- Sasikumar, K., & Nagarajan, S. (2024). Comprehensive Review and Analysis of Cryptography Techniques in Cloud Computing, IEEE Access.
- Coelho, K. K., Nogueira, M., Marim, M. C., Silva, E. F., Vieira, A. B., & Nacif, J. A. M. (2022). Lorena: Low memory symmetric-key generation method for based on group cryptography protocol applied to the internet of healthcare things, IEEE Access, 10, 12564-12579.
- Mohammed, M. A., Abood, L. K., & Maliki, M. (2016). MMAC: Fast and Secure Message Authentication, International Journal of Science and Research (IJSR), 6(12), 576-579.
- Gupta, C., & Reddy, N. S. (2022). Enhancement of Security of Diffie-Hellman Key Exchange Protocol using RSA Cryptography, In Journal of Physics: Conference Series, 2161(1), IOP Publishing.
- Archana, B., U., & Niranjana, V. (2023). Overview of Cryptography, 2, doi: 10.46632/daai/3/2/15
- Zaryab, A. (2022). Cryptology Based on Laplace Transform of Hyperbolic Function and Matrix Decomposition Method, Meeting abstracts, doi: 10.1149/ma2022-02642364mtgabs.
- Zhao, Y., He, J., Shu, Q., & Yang, S. (2015). Advanced encryption standard (AES) secret key generation structure based on physical unclonable function (PUF) of latch-type voltage sensitive amplifier.
- Stein, Y., & Kablotsky, J. A. (2008). U.S. Patent No. 7,421,076. Washington, DC: U.S. Patent and Trademark Office.
- Modi, T., Patel, J., Paliwal, M., Shah, K., & Shastri, A. (2023, March). Enhancing Medical Domain Data Security using Inbuilt Data Encryption and Steganography, In 2023 10th International Conference on Computing for Sustainable Global Development (INDIACom) (pp. 181-187). IEEE.
- Fatima, S., Hussain, S., Shahzadi, N., ul Din, B., Sajjad, W., Saleem, Y., & Aun, M. (2022, December). A Secure Framework for IoT Healthcare Data Using Hybrid Encryption, In 2022 International Conference on Emerging Trends in Electrical, Control, and Telecommunication Engineering (ETECTE) (pp. 1-7). IEEE.
- Babatunde, A. O., Taiwo, A. J., & Dada, E. G. (2018). Information security in health care centre using cryptography and steganography. arXiv preprint arXiv:1803.05593.
- El Bouchti, A., Bahsani, S., & Nahhal, T. (2016, August). Encryption as a service for data healthcare cloud security, In 2016 fifth international conference on future generation communication technologies (FGCT) (pp. 48-54). IEEE.
- Okpu, E. O., Taylor, O. E., Nwiabu, N. D., & Matthias, D. (2024).Comparative Performance Analysis of Cryptographic Techniques for Securing the Physical Layer in Internet of Medical Things (IoMT) Systems,International Journal of Computer Science and Mathematical Theory (IJCSMT) E-ISSN 2545-5699, 10(2), 157-170.
- Zhang, R., Xue, R., & Liu, L. (2017). Searchable encryption for healthcare clouds: A survey, IEEE Transactions on Services Computing, 11(6), 978-996.
- Sowmiya, L., Rajasekaran, A. S., Suganyadevi, S., Sureshkumar, S., Subramaniam, G., & Jaazieliah, R. (2023, February). A Secure Authenticated Message Transfer in Healthcare Application, In 2023 IEEE International Conference on Integrated Circuits and Communication Systems (ICICACS) (pp. 1-6). IEEE.
- Prabhu, A. J., & Rajesh, D. H. (2023). Authentication of WSN for Secured Medical Data Transmission Using Diffie Hellman Algorithm, Computer Systems Science & Engineering, 46(1).
- Lim, C. K., Iipinge, V. J., Tan, K. L., & Hambira, N. (2018, November). Design and development of message authentication process for telemedicine application, In 2018 IEEE Conference on Wireless Sensors (ICWiSe) (pp. 23-28). IEEE.
- Khan, M. A., Quasim, M. T., Alghamdi, N. S., & Khan, M. Y. (2020). A secure framework for authentication and encryption using improved ECC for IoT-based medical sensor data, IEEE Access, 8, 52018-52027.
- Patgiri, R. (2021). Privatedh: An enhanced diffie-hellman key-exchange protocol using RSA and AES algorithm, Cryptology ePrint Archive.
Eterigho Okpomo Okpu

Pursued B.Sc. degree in Computer Science at Delta State University, Abraka, MSc and PhD at Rivers State University. He is currently a Lecturer in the Department of Cyber Security, Delta State University of Science & Technology, Ozoro. He is a member of the Computer Professionals of Nigeria (CPN). His research works focuses on Machine Intelligence Systems, Cyber Security, & IoT. (ORCID iD: https://orcid.org/0009-0004-0116-4506).
Onate Egerton Taylor
Pursued B.Sc. degree in Computer Science at Rivers State University, MSc at the University of Ibadan, & PhD at the University of Port Harcourt. He is currently an Associate Professor & a Lecturer in the Department of Computer Science, Rivers State University, Port-Harcourt. He is a member of the Computer Professionals of Nigeria (CPN). He has published over 50 research papers in reputed international journals. His research works focuses on Machine Intelligence Systems, Cyber Security, & IoT. (ORCID iD: https://orcid.org/0009-0004-0116-4506).
